TECHNICAL SPECIFICATIONS
// PROTOCOL_SPECIFICATION_v2.0 // CROSS-DOMAIN_AI_HARDENING // IOT_EDGE_ENABLED
AGENTIC HARDENING
Zero-Trust enforcement at the state-transition level. Neutralizes risks in LangGraph, LangSmith, and MCP nodes by treating every 'Edge' as a security perimeter.


COMPONENT_01 // AGENT_SECURITY
> NODE_ISOLATION_ACTIVE
> EDGE-GATE_INTERCEPTION
> PROTOCOL_PROXY_ENFORCED
COMPONENT_02 // DATA_INTEGRITY
GENAI & RAG INTEGRITY
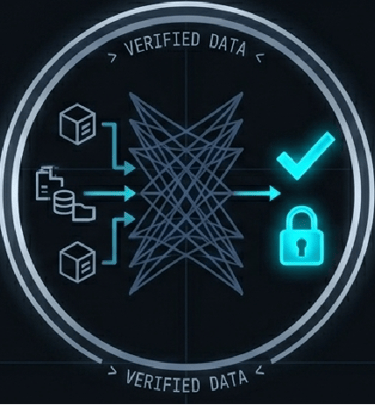
Cryptographic verification layer between retrieval and model. Ensures data provenance and prevents vector-base manipulation during RAG cycles.
> ATTESTATION_DIGESTS
> RETRIEVAL_SCRUBBING
> ANTI-POISONING_PROTOCOL
COMPONENT_03 // IOT_SECURITY
AI & IOT EDGE SECURITY
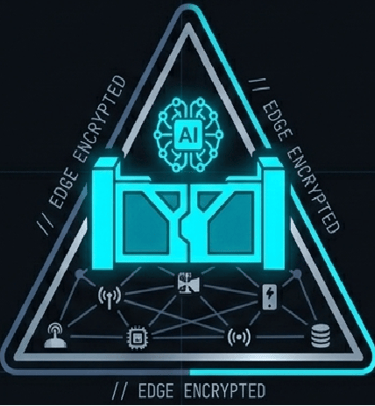

Hardens the interface between physical sensors and intelligence layers. Ensures edge inference cannot be manipulated to cause system-wide failure.
> DEVICE_CONTAINMENT
> DETERMINISTIC_RECONSTITUTION
> HARDWARE-LEVEL_SAFE_STATE
[O] OUTPUT-LOGIC ENFORCEMENT
> ACTION-GATE VALIDATION: ACTIVE
> DETERMINISTIC COMPLIANCE CHECK: 100%
> CRYPTOGRAPHIC FORENSIC LOGGING: ENABLED
PROTOCOL DEPLOYMENT ARCHITECTURE
[C] CONTAINMENT
// DOMAIN_ENFORCEMENT_V1.3
> AGENTIC / IoT / GENAI
// STATUS: ACTIVE
> GEN-AI: Isolation of prompt-context to prevent data-leakage.
> AGENTIC-AI: Sandboxing of LangGraph nodes to block lateral escalation.
> AI & IOT: Air-gapped execution of model inference on edge hardware.
[A] ATTESTATION
// PROVENANCE_VERIFICATION_V1.3
> IDENTITY / TRUST / SOURCE
// STATUS: ENFORCED
> GEN-AI: Cryptographic verification of PDF/Vector source provenance (Anti-Poisoning).
> AGENTIC-AI: Identity-check of Agentic "Intent" before granting tool-access.
> AI & IOT: Mutual TLS and device-identity verification for sensor-to-model feeds.
[I] INTERCEPTION
// TRAFFIC_SCRUBBING_V1.3
> INJECTION / MONITOR / DRIFT
// STATUS: MONITORING
> GEN-AI: Real-time scrubbing of user inputs for Indirect Prompt Injection.
> AGENTIC-AI: Monitoring of LangGraph Edge-transitions to stop unauthorized tool-calls.
> AI & IOT: Behavioral analysis of telemetry data to detect sensor manipulation.
[R] RECONSTITUTION
// SYSTEM_RECOVERY_V1.3
> ROLLBACK / RESET / HEAL
// STATUS: STANDBY
> GEN-AI: Automated cache-clearing and session-reset if hallucination thresholds met.
> AGENTIC-AI: "Safe-State" rollbacks for agents exceeding pre-defined boundaries.
> AI & IOT: Hardware-level firmware recovery if AI-driven controller exhibits failure.
[O] OUTPUT-LOGIC
// DETERMINISTIC_GATE_V1.3
> COMPLIANCE / PII / ACTION
// STATUS: ACTIVE
> GEN-AI: Deterministic PII-redaction and compliance-check of all generated text.
> AGENTIC-AI: Hard-gate validation of all API/SQL writes before system execution.
> AI & IOT: Binary "Go/No-Go" logic for physical actuators based on governance.
// FRAMEWORK_ALIGNMENT: NIST AI RMF v1.0 // ISO/IEC 42001:2023 // CAIRO_PROTOCOL_ENFORCED
VALIDATE YOUR INFRASTRUCTURE
Modern AI risks—from Prompt Injection and Data Poisoning to Agentic Privilege Escalation—cannot be solved with probabilistic filters. They require deterministic, infrastructure-level hardening. Ensure your LangGraph nodes, MCP gateways, and IoT edge-points meet the highest standards of the CAIRO Protocol.
INITIATE ARCHITECTURAL REVIEW
Secure your GenAI infrastructure and Agentic workflows against the next generation of threats. Available for high-tier audits and strategic advisory.
Call
info@cairoprotocol.com
+91-9600101449
© 2026 // ALL_RIGHTS_RESERVED // HARDENED_BY_CAIRO_PROTOCOL